The main weapon of a real hacker is his brain. But even the best brain will not give up these gizmos. We present you the gadgets that every self-respecting hacker should have.
These gadgets will be especially useful for beginners. Grab a pen and take notes!
Raspberry PI 4
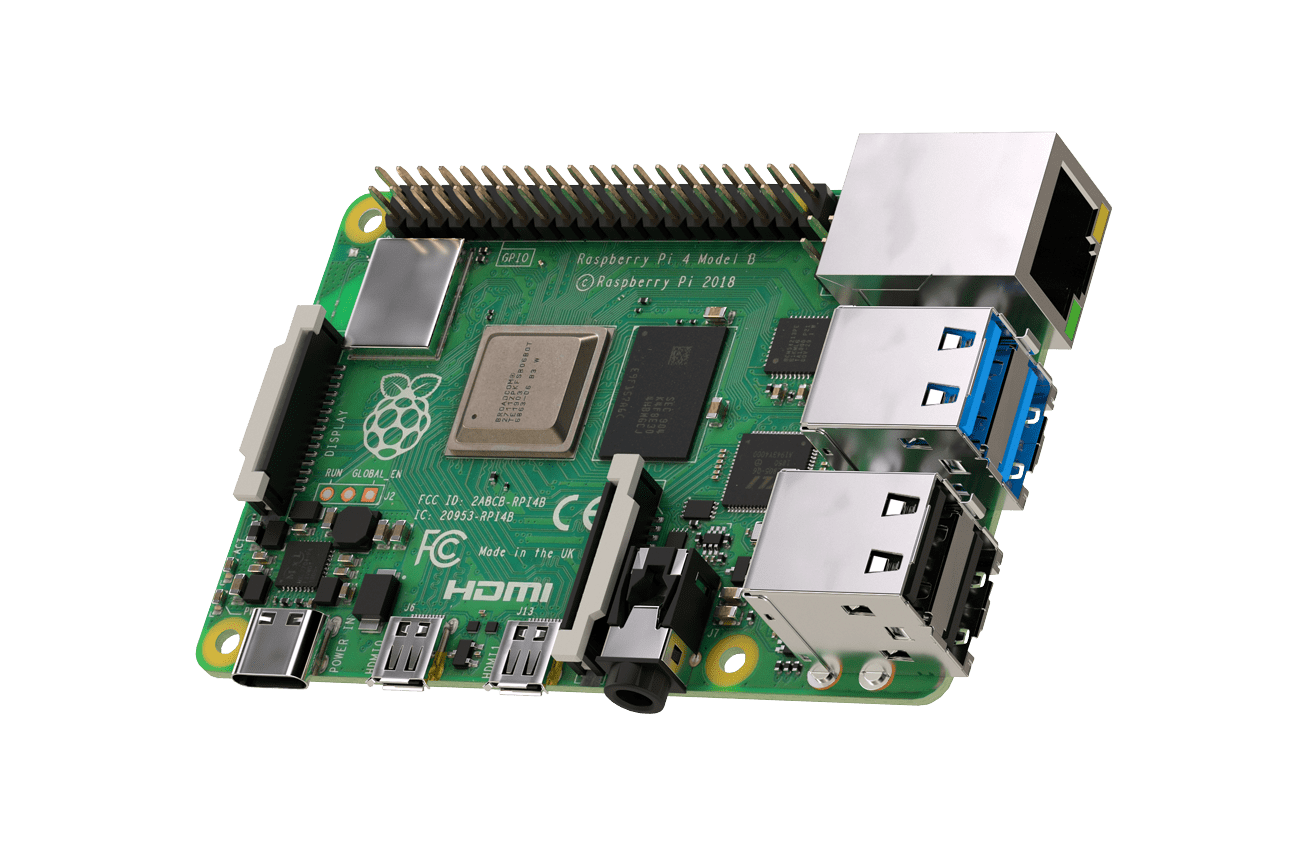
The Raspberry PI 4 is the fourth generation single board computer. The gadget is a little bigger than a plastic card, but with more ports available. Such as, HDMI, DSI, USB 2.0. Simply plug in a mouse, keyboard, SD card with Linux distribution installed and connect the power via Micro USB. The Raspberry can replace an inexpensive office desktop, which is often used to create media centers and home servers, and in other projects from musical instruments to robots. But that’s not what interests us: the Raspberry could be the perfect system for pentests in the field. And there are plenty of off-the-shelf enclosures, displays, batteries, and other hardware. As well as the software we can run on them. What about Kali Linux?
This powerful hacker’s weapon is only $35. Its usefulness is in its size. After all, you can take (or stick, for example) a Raspberry PI where you can’t sneak a laptop.
Proxmark3

The best device to perform an attack on contactless cards remains Proxmark3. It is available in several variants. There are several offers on the market, but the most common, cheapest and affordable is RDV3. There are also Chinese clones of the device. There is a “but”, this tool is not for beginners. The Proxmark III is a de facto RFID research tool. There are others, but none of them even come close in prevalence or community support to PM3. Proxmark III is capable of reading, writing and even emulating most of the currently available RFID tags, including payment cards that also work with RFID. Having doubts? Check out the firmware on the forum at http://proxmark.org/forum/index.php.
HackRF One

HackRF is a unique device designed for enthusiasts and radio amateurs who are passionate about studying radio signals and everything related to it. At the moment there are more advanced devices, but HackRF One, which can be easily ordered from the Chinese, is the best price solution for beginners who want to understand what SDR is. What makes HackRF unique is its technical parameters – at less than $100, the device not only allows you to receive but also transmit radio signals in the 1MHz-6GHz range with a bandwidth up to 20MHz. Unfortunately, HackRF is not a full-fledged radio station, its power is too low and is about 20 mW, and the efficiency of the regular antenna is less than 1%.
LAN Turtle

LAN Turtle is a tiny network infiltration implant disguised as a USB-Ethernet adapter. Easily set up with the built-in graphical shell and deploy payloads such as DNS poisoning attacks, MITM, network scanning, VPN tunneling, etc. Oh yes, it all works remotely, directly over 3G.
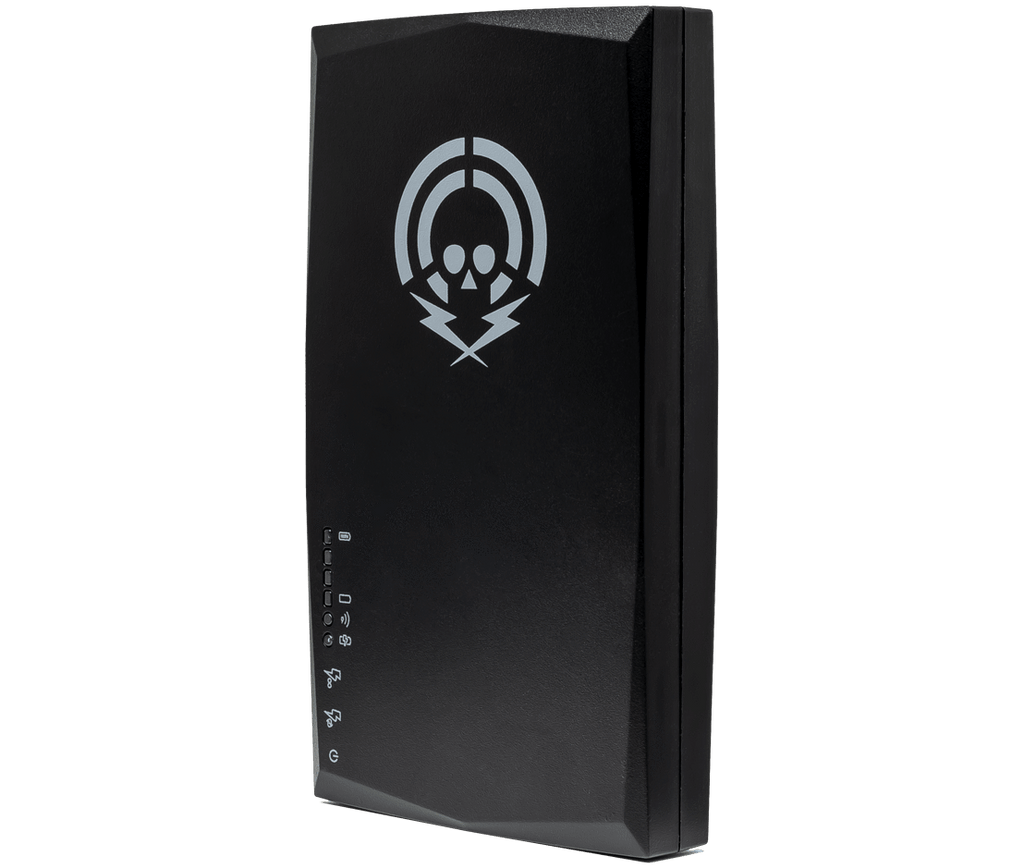
WiFi Pineapple

It is a wireless MITM attack kit, perfected to perfection. WiFi Pineapple is a real combine designed by some clever Americans, who modified the OpenWRT firmware specifically for it and literally stuffed it with a lot of various utilities and programs for hacking and intercepting information in wireless networks. The capabilities of the device are really impressive.
MagSpoof

Magspoof – any credit card emulator.
When working with magnetic cards, many people face the same problem: a three-strip card reader with recording capability sometimes costs five times more than the same reader without recording capability. MagSpoof board was developed for such tasks, on which the data of three magnetic stripes can be written and spoofed. Thus the device replaces a real card. And in combination with a magnetic card reader you will save half the money and get a complete device to test the security of the pass or payment system.
Ubertooth One

Ubertooth One is a 2.4 GHz wireless research platform for experimenting with Bluetooth. Thanks to the powerful LPC175x ARM Cortex-M3 processor, the capabilities of the device far exceed those of a conventional adapter, allowing you to intercept and monitor, jam or even modify the signal from other devices. It is a fully open-source platform with a developed ecosystem.
Alfa AWUS036NH

Alfa AWUS036NH is a legendary adapter that breaks communication range records. With it, you can warp access points not only at your neighbor’s, but also in another building. This adapter uses the well-proven Ralink RT3070 chipset, which works great under Kali Linux. Cheaper Chinese analogues on the same chip are available, not significantly different in quality.
O.MG cable
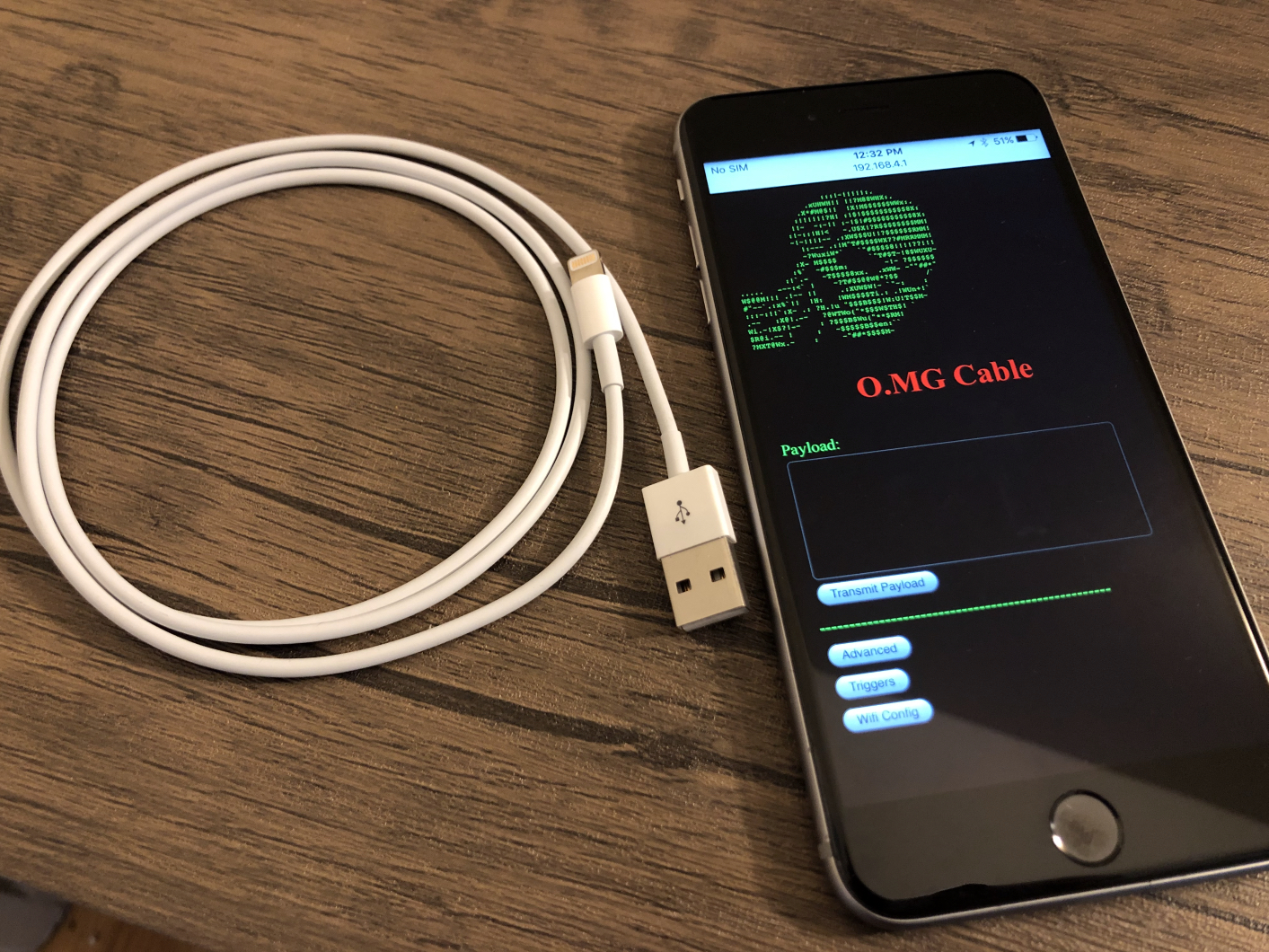
Have you heard of the Rubber Ducky, which allows you to emulate a keyboard and enter arbitrary commands when connected to the victim’s computer? Well, imagine having a full-fledged Rubber Ducky embedded in an ordinary-sized cable, moreover, controlled via Wi-Fi and allowing you to remotely enter keyboard commands into the device connected to it. O.MG is indistinguishable from the usual charging cable. The device comes in several variants: Type-C, micro-USB and Lightning.
FaceDancer21

The FaceDancer21 device is a must-have tool for the tester of payment terminals. With it you can emulate different USB devices. For example, to create a device with a certain ID and bypass the list of allowed connectable devices, to determine what types of devices the USB port supports, which is useful when working with ATMs and wireless chargers (in case the wireless charger is a small computer port), to phase. which is convenient for searching 0day in USB drivers. True to its name, FaceDancer lets you not only change device IDs, but also mask “hosts” as separate USB devices and vice versa. But that’s not all. The main advantage of the device is that it allows access to the USB bus using high-level programming languages via Puthon, C and Ruby libraries. Knowing the API, an intruder can easily gain access to the ATM host by spoofing the controller ID and directly control peripherals inside the ATM, such as the cash dispenser.
Yard Stick One

If you’ve tried unlocking your car lock by repeating the unlock signal, you might appreciate this device. Yard Stick One allows you to send and receive traffic on popular frequencies (up to 1 GHz). Its distinctive feature is the use of the CC1111 chip, which allows you to hardware demodulate or modulate the signal, which improves the quality of reception and transmission. You will need to install the free RFCat utility to work with the Yard Stick. Still have doubts? In 2018, researchers showed how they hijacked a Tesla Model S using a Raspeberry PI, Yard Stick One and Proxmark III. Even if you can’t get it open – you can always jam it.
NFC Kill
Not many people can be surprised by contactless card testing devices these days. But the NFC Kill device will definitely interest you: first of all, it is designed for phasic testing of contactless reader systems. And additional features allow to disable both readers and contactless cards themselves. The device works on three frequencies: Low Frequency (125-134 kHz), High Frequency (13.56 MHz) and Ultra High Frequency (850-930 MHz). It comes in two versions: Standard and Professional. The difference between them is the ability to run tests without physical interaction with the device.
Bash Bunny

Chances are you’re already familiar with Rubber Ducky, a device that emulates a keyboard and injects malicious commands into a victim’s computer. The Bash Bunny is an advanced version of the HID attack device. In addition to a keyboard, it can emulate any serial port devices, file storages, and USB to Ethernet adapters. This device is great for Red Team tests and saves money and space in your camping kit.
Hunter Cat
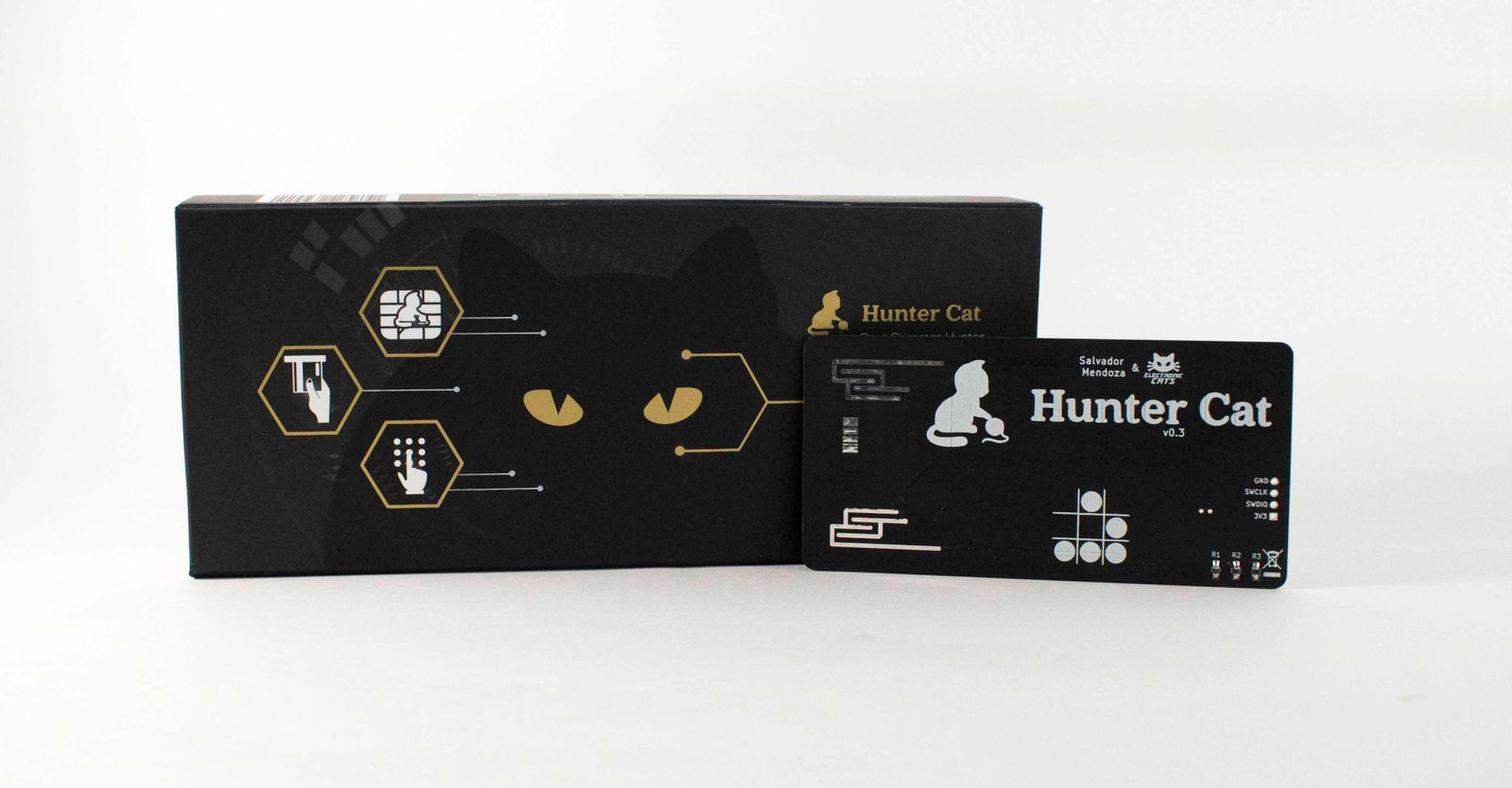
In 2019, an interesting device appeared on the market – Hunter Cat. It was developed to search for bank and other skimmers. Its essence is simple: you insert it into the card acceptor, take it out and look at the LED. If it glows green, the skimmer is not detected, otherwise it is better not to use this ATM. The Hunter Cat is slightly larger than a bank card and costs about $35. Especially useful will be such a device when traveling in Asia and third world countries.
Whether you are a beginner or an advanced hacker, you need to evolve, learn and always experiment. And our editorial staff will always keep you up to date. Stay tuned and ask your questions in the chat room. See you soon.
Never use the methods described in the article. This article is written for informational purposes only. The author is not responsible for the application of the skills. Otherwise, you are breaking the law.